
Introduction
A manufacturing plant's SCADA system controlling critical processes is suddenly compromised. Production grinds to a halt. Safety systems fail. The financial impact spirals into hundreds of thousands of dollars per hour.
This scenario isn't hypothetical. In 2024, industrial organizations experienced an 87% surge in ransomware attacks, with 75% causing partial operational shutdowns and 25% forcing complete production halts.
SCADA (Supervisory Control and Data Acquisition) systems form the backbone of critical infrastructure across utilities, manufacturing, water treatment, and energy sectors. Yet the same connectivity that enables remote monitoring and control has dramatically increased their vulnerability to cyber threats.
As IT and OT networks converge, the attack surface expands—40% more ICS devices became internet-exposed between 2024 and 2025 alone.
This article examines why SCADA security differs significantly from traditional IT security, explores the current threat landscape, and provides actionable best practices for protecting critical infrastructure from advanced cyberattacks.
TLDR:
- SCADA systems prioritize availability and safety over confidentiality, requiring specialized security approaches distinct from traditional IT
- Ransomware attacks on industrial systems surged 87% in 2024, with 75% causing operational shutdowns
- Legacy systems running outdated operating systems and insecure protocols create persistent vulnerabilities
- Network segmentation (Purdue Model) and Zero Trust controls form the foundation of SCADA security
- Regular security assessments by qualified engineers who understand both cybersecurity and industrial operations are essential
What Is SCADA and Why Security Matters for Critical Infrastructure
SCADA (Supervisory Control and Data Acquisition) systems monitor and control physical processes across critical infrastructure—from power grids to water treatment plants. Unlike traditional IT systems where data confidentiality is paramount, SCADA security prioritizes availability and safety.
Compromises can lead to physical damage, environmental hazards, or loss of life.
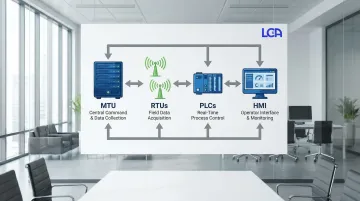
Core SCADA Architecture
A SCADA system integrates data acquisition with transmission and Human-Machine Interface (HMI) software to provide centralized control. The architecture relies on four primary components:
- Master Terminal Unit (MTU): The central server at the control center that collects field data, processes it, and issues commands to remote sites
- Remote Terminal Units (RTUs): Field devices designed for remote telemetry that collect sensor data and control actuators, often communicating wirelessly
- Programmable Logic Controllers (PLCs): Industrial computers performing logic functions to control local processes
- Human-Machine Interface (HMI): Software interface allowing operators to visualize process states, configure set points, and intervene in control algorithms
The IT/OT Convergence Challenge
SCADA systems were historically air-gapped—physically isolated from corporate networks and the internet. This isolation provided inherent security through obscurity.
IT/OT convergence has fundamentally changed this landscape. Organizations now connect SCADA systems to corporate networks for data analytics, remote monitoring, and operational efficiency. This connectivity creates direct pathways for attackers.
Recent research reveals the scale of the problem:
- 40% more ICS devices exposed to the internet between 2024 and 2025
- 65% of assessed sites had insecure remote access conditions
- Default credentials and unpatched VPNs remain common vulnerabilities
Why SCADA Security Differs from Traditional IT
SCADA security requires fundamentally different approaches than traditional IT security:
- Availability vs. Confidentiality: IT security prioritizes protecting data from unauthorized access. SCADA security prioritizes availability and safety—a compromised water treatment plant or power grid poses immediate physical risks
- Real-Time Operations: SCADA systems operate with strict timing requirements. Security measures cannot introduce latency that disrupts control loops or safety systems
- Legacy Equipment: OT environments frequently operate equipment with lifecycles exceeding 20 years, often running unsupported operating systems like Windows XP that cannot be patched
- Physical Safety: Cyberattacks on SCADA systems can cause physical damage to equipment, environmental contamination, or endanger human life—consequences rarely present in traditional IT breaches
The Financial and Operational Impact
The cost of SCADA-related cyberattacks has escalated dramatically:
- 45% of organizations affected by cyber-physical attacks suffered losses of $500,000 or more
- 27% reported losses exceeding $1 million
Beyond direct financial impact, operational disruptions cascade through supply chains and communities. The 2021 Colonial Pipeline ransomware attack compromised IT systems but forced OT shutdown as a precaution.
The result: fuel shortages across the U.S. East Coast that demonstrated how cyber threats to industrial systems create consequences far beyond the targeted organization.
SCADA vs. ICS vs. OT: Understanding the Terminology
Precise terminology is essential for defining security scope and regulatory compliance. These terms are often used interchangeably but have distinct meanings.
Hierarchical Relationship
The three terms form a hierarchy, with each level narrowing in scope:
- Operational Technology (OT): The broadest category, including all hardware and software that detects or causes change through direct monitoring and control of physical devices, processes, and events
- Industrial Control Systems (ICS): A subset of OT that includes various control system types used in industrial production—SCADA, Distributed Control Systems (DCS), and PLCs
- SCADA: A specific ICS type for monitoring geographically dispersed assets where centralized data collection is critical (pipelines, power grids, water distribution networks)
- Distributed Control Systems (DCS): Unlike SCADA, DCS controls production systems within a local area such as a factory or refinery
Why These Distinctions Matter for Security
Understanding these distinctions shapes security strategy. SCADA systems spanning hundreds of miles face different threats than DCS systems controlling a single production line.
SCADA security must account for wireless communications, remote site vulnerabilities, and wide-area network risks that may not apply to localized DCS implementations.
OT security covers the entire operational environment, while SCADA security focuses specifically on supervisory control and data acquisition components. Implementing appropriate security measures requires understanding exactly which systems you're protecting and their specific vulnerabilities.
The SCADA Threat Landscape: Real Risks to Critical Infrastructure
SCADA systems face real, documented threats. The landscape has evolved from theoretical vulnerabilities to sophisticated, coordinated attacks capable of causing physical damage and widespread disruption.
Threat Actors and Their Motivations
Nation-State Actors conduct espionage and position themselves for potential disruption of critical infrastructure during geopolitical conflicts. These adversaries possess advanced capabilities and long-term persistence.
Cybercriminals target industrial organizations with ransomware for financial gain. Industrial victims often pay higher ransoms due to the severe operational and safety consequences of downtime.
Insider Threats are disgruntled employees or contractors with legitimate access who can cause significant damage through sabotage or data theft.
Hacktivists seek to disrupt operations or make political statements by targeting organizations whose activities they oppose.
Landmark SCADA Attacks and Lessons Learned
| Attack | Year | Target | Impact | Key Lesson |
|---|---|---|---|---|
| Stuxnet | 2010 | Iranian Nuclear Centrifuges | Physical damage to centrifuges through PLC code manipulation | Air-gapped systems aren't immune; USB-borne malware can bridge the gap |
| Ukraine Power Grid | 2015 | Ukrainian Electric Distribution | Power outages affecting 225,000 customers | Phishing targeting OT personnel provides initial access; attackers studied systems for months before striking |
| Colonial Pipeline | 2021 | U.S. Fuel Pipeline | Major fuel supply disruptions across East Coast | Compromised VPN credentials enabled access; even IT-focused attacks can force OT shutdowns |

Current Threat Intelligence
Threat actors are increasingly positioning themselves for operational impact. In 2025, 4% of OT vulnerabilities were actively exploited, and 26 active OT threat groups were tracked, including three newly emerged groups.
Adversaries have moved beyond reconnaissance to actively mapping control loops, demonstrating intent to manipulate physical processes.
Common Attack Vectors
Industrial facilities face multiple attack vectors:
- Phishing targeting OT personnel — Social engineering campaigns reference equipment vendors or operational issues to target control engineers and operators
- Supply chain compromises — Threat groups target third-party vendors and software packages to gain indirect access to multiple downstream victims
- Internet-facing HMIs — Many organizations unknowingly expose HMIs to the internet, where attackers exploit default credentials or known vulnerabilities
- USB-borne malware — Despite Stuxnet's lessons, USB drives remain a threat in air-gapped environments used to transfer updates and configuration files
- Remote access vulnerabilities — Unpatched VPNs and exposed RDP sessions are widespread, with 65% of assessed sites exhibiting these vulnerabilities
Common SCADA Security Vulnerabilities
Most SCADA systems controlling critical infrastructure weren't built with cybersecurity in mind. These environments often rely on decades-old technology and protocols that lack basic security features, creating multiple attack vectors for threat actors.
Legacy System Vulnerabilities
Industrial facilities commonly run equipment for 20+ years, far exceeding typical IT refresh cycles. This extended lifespan creates significant security gaps:
- Unsupported operating systems like Windows XP and legacy Unix versions that no longer receive security updates
- Controllers and field devices with firmware that cannot be updated without halting production
- Default passwords embedded in firmware that cannot be changed
- Systems transmitting sensitive process data without encryption
These "forever day" vulnerabilities cannot be patched, requiring compensating controls like network isolation to secure them.
Insecure Industrial Protocols
The communication backbone of most SCADA systems relies on protocols designed 30+ years ago. Modbus, DNP3, and similar protocols remain industry standard but lack fundamental security features:
- No authentication requirements, allowing any network-connected device to issue commands to PLCs and RTUs
- Unencrypted data transmission that attackers can intercept and read
- No integrity checks, making protocols vulnerable to spoofing and replay attacks
Network Architecture Weaknesses
Beyond protocol vulnerabilities, many SCADA networks suffer from poor architectural design. Flat network structures with inadequate segmentation create multiple security risks:
- Flat networks without security zones that let attackers move laterally after initial breach
- Internet-exposed SCADA components with inadequate firewall protection
- Weak boundaries between corporate IT and OT networks that allow attackers to pivot from office systems into control networks
- Limited visibility and monitoring capabilities, with many vulnerabilities buried deep within networks where they're difficult to detect
Human Factor Vulnerabilities
Even well-designed technical controls can't compensate for human vulnerabilities. Personnel gaps create some of the most exploitable weaknesses:
- OT personnel often lack cybersecurity awareness training specific to industrial environments
- Excessive privileges, shared accounts, and inadequate access reviews
- Continued use of factory default passwords on critical equipment
- Limited awareness of phishing and social engineering tactics targeting OT personnel
Vendor and Third-Party Risks
External parties with access to SCADA systems create additional attack vectors:
- Equipment vendors requiring remote access for maintenance, often using insecure connection methods
- Compromised vendor software or hardware that can introduce backdoors into critical systems
- Procurement processes that fail to enforce security standards for new equipment
SCADA Security Standards and Compliance Frameworks
Security frameworks give manufacturing and industrial facilities a proven roadmap to protect SCADA systems from cyber threats.
NERC CIP Requirements
For the electric utility sector, the North American Electric Reliability Corporation (NERC) Critical Infrastructure Protection (CIP) standards are mandatory. Key standards include:
- CIP-003: Security Management Controls establishing organizational security policies
- CIP-005: Electronic Security Perimeters defining boundaries between trusted and untrusted networks
- CIP-007: System Security Management covering patching, ports, and malware prevention
- CIP-010: Configuration Change Management ensuring controlled modifications
- CIP-013: Supply Chain Risk Management addressing vendor and procurement risks
IEC 62443 Standard Series
ISA/IEC 62443 serves as the global standard for securing Industrial Automation and Control Systems (IACS):
- ISA-62443-2-1: Defines security program requirements for asset owners
- ISA-62443-3-2: Provides guidance on risk assessments and defining security zones and conduits
- ISA-62443-3-3: Specifies detailed system security requirements and security levels
- ISA-62443-4-1/4-2: Focuses on secure product development lifecycles and technical requirements for components
NIST Cybersecurity Framework
The NIST Cybersecurity Framework provides a flexible structure for managing cybersecurity risk. NIST SP 800-82 provides specific guidance on mapping the framework to OT environments, helping organizations align SCADA security strategies with broader enterprise risk management.
Selecting Applicable Standards
Industries face varying regulatory requirements based on their sector:
- Electric utilities: Must comply with NERC CIP (mandatory)
- Water/wastewater systems: Follow EPA guidance and CISA recommendations
- Manufacturing facilities: Adopt IEC 62443 voluntarily or based on customer requirements
- Chemical plants: May require CFATS compliance for high-risk facilities
The business case for compliance extends beyond avoiding penalties. A food manufacturer implementing IEC 62443 reduced unauthorized network access attempts by 73% within six months. Standards provide proven frameworks that reduce risk, demonstrate due diligence to customers and insurers, and establish security baselines protecting both operations and reputation.
Best Practices for Securing SCADA Networks
Network Segmentation and Defense in Depth
Effective segmentation is the most critical control for limiting the blast radius of a cyberattack.
The Purdue Model for ICS Security
The Purdue Model organizes ICS networks into hierarchical levels to enforce segmentation:
- Level 0: Physical Process (sensors, actuators)
- Level 1: Basic Control (PLCs, controllers)
- Level 2: Supervisory Control (SCADA, HMI)
- Level 3: Manufacturing Operations (MES, Historian)
- Level 4/5: Enterprise and Corporate IT networks
Each level should have controlled data flows to adjacent levels only, with firewalls enforcing strict rules about what traffic is permitted between zones.
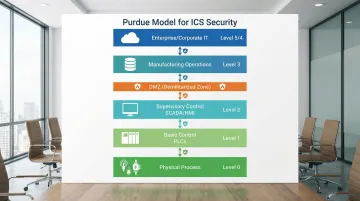
DMZ Implementation
A Demilitarized Zone (DMZ) separates IT (Levels 4-5) from OT (Levels 0-3). This buffer zone hosts shared services like historians or patch servers, preventing direct traffic between corporate and control networks.
Data Diodes and Unidirectional Gateways
For high-security environments, data diodes provide hardware-enforced one-way communication paths. They allow data to flow out of the secure OT network for monitoring but physically prevent any data or attacks from entering.
This ensures that even if the external network is compromised, the critical control network remains isolated.
Access Control and Authentication
Zero Trust Principles Adapted for OT
Zero Trust assumes no user or device is trustworthy by default. While safety functions must never be impeded, Zero Trust principles can be applied to:
- Verify explicitly: Continuously authenticate users and devices
- Least privilege: Grant only the minimum access necessary for a role
- Assume breach: Monitor for anomalies as if the network is already compromised
Multi-Factor Authentication (MFA)
MFA provides critical defense against credential theft. Enforce it for all remote access connections and administrative access to critical systems.
Legacy devices may not support MFA directly, but you can implement it at the network level via VPN concentrators.
Role-Based Access Control (RBAC)
Implement RBAC specific to SCADA environments:
- Define roles based on operational responsibilities
- Operators need different access than engineers
- Engineers need different access than maintenance personnel
- Align permissions with actual job functions
Managing Vendor and Contractor Access
Third-party vendors often require remote access for maintenance. Best practices include:
- Establishing clear security requirements in Service Level Agreements
- Using secure, monitored communication channels (VPNs with MFA)
- Implementing "just-in-time" access enabled only during specific maintenance windows
- Logging and reviewing all vendor access sessions

Continuous Monitoring and Threat Detection
OT-Specific Security Monitoring Tools
Standard IT monitoring tools can disrupt sensitive SCADA equipment. OT-specific solutions use passive monitoring and Deep Packet Inspection to analyze industrial protocols without interfering with operations.
Behavioral Analysis and Anomaly Detection
Industrial processes follow predictable patterns. This makes behavioral analysis particularly effective.
Security tools establish a baseline of "normal" traffic—such as a PLC reading a specific register every 5 seconds—and alert on deviations like unexpected commands or new communication flows.
Asset Inventory and Network Traffic Analysis
You cannot protect what you don't know exists. Comprehensive asset inventory identifying every device, its function, communication patterns, and vulnerabilities is foundational. Network traffic analysis provides visibility into actual communication patterns versus intended architectures.
SOC Integration
Integrating OT monitoring into a Security Operations Center provides unified threat visibility. However, SOC analysts must be trained on ICS-specific playbooks to avoid actions that could disrupt physical processes.
Patch Management and Vulnerability Management
The Challenge of Patching Legacy SCADA Systems
In OT, availability often trumps the need for immediate patching. Prioritize patches using this risk-based approach:
- "Now": Critical vulnerabilities on internet-facing or perimeter devices
- "Next": High-priority issues addressed during planned outages
- "Never": Low-risk vulnerabilities on isolated systems where patching introduces operational risk
Virtual Patching and Compensating Controls
When patching isn't feasible on legacy systems, compensating controls are required. Virtual patching uses network intrusion prevention systems to block exploit traffic targeting specific vulnerabilities, protecting unpatched devices without modifying them.
Testing Patches in Isolated Environments
Patches must be rigorously tested in offline or test environments mirroring production to ensure they don't cause system instability or safety issues.
Strategic System Modernization
Many organizations need expert guidance to modernize aging SCADA infrastructure. Controls integration firms like Lashley Cohen & Associates help manufacturers upgrade legacy systems and implement security enhancements during planned modernization projects. Their ISO-9001 certified processes and 35+ years in industrial automation enable strategic transitions from vulnerable legacy systems to modern architectures without compromising production continuity.
Incident Response Planning
OT-Specific Incident Response Plans
Incident response plans for SCADA must prioritize safety and physical process stability. Plans should define clear roles for OT personnel who understand physical systems and can manually override controls if necessary.
Coordinating IT and OT Teams
Effective response requires seamless coordination between IT and OT teams. IT responders must understand that standard containment tactics like isolating a server can have catastrophic physical consequences in OT environments. Joint training and tabletop exercises are essential to bridge this operational gap.
Security Assessments and Continuous Improvement
Regular security assessments require engineering professionals who understand both cybersecurity and industrial control systems. Certified PE engineers can identify vulnerabilities specific to manufacturing environments.
They provide actionable remediation roadmaps that account for operational constraints and safety requirements.
These assessments should evaluate network architecture, access controls, monitoring capabilities, patch management processes, and incident response readiness. The goal isn't just identifying vulnerabilities but prioritizing them based on operational impact and providing practical remediation strategies that maintain production continuity.
Industry-Specific SCADA Security Considerations
Water and Wastewater Systems
The water sector directly impacts public health. Attacks that alter chemical dosing, disable treatment processes, or compromise distribution systems can affect entire communities.
Regulatory Environment: EPA and CISA provide specific guidance for securing water systems.
Recent attacks, such as the one on American Water in 2024, highlight the sector's vulnerability and the need for strong security measures.
Security Priorities for water systems:
- Ensure integrity of treatment processes
- Protect against tampering that could affect water quality
- Maintain availability of critical services
- Monitor chemical feed systems and treatment parameters for anomalies
Manufacturing
Manufacturing environments face unique challenges securing diverse proprietary protocols and legacy controllers. The sector sees the most ransomware attacks, with incidents frequently causing production stoppages.
Operational Continuity: Security strategies must account for the high cost of downtime. A single production line stoppage can cost hundreds of thousands of dollars per hour, making availability the top priority.
Complex Environments: Manufacturing facilities often run dozens of different control systems from various vendors, each with different security requirements.
Securing these mixed environments requires deep knowledge of multiple platforms and protocols.
Food and Beverage
In food and beverage, SCADA security directly affects product safety and regulatory compliance (FDA, USDA). Integrity attacks that alter recipes or temperature controls can lead to spoilage or unsafe products.
Critical Protection Areas:
- Data integrity for traceability and compliance records
- Batch records and quality data (compromises create regulatory and liability issues)
- Temperature controls and pasteurization systems
- Recipe management systems that control product formulation
Security breaches in food manufacturing create risks beyond operational disruption—they can compromise consumer safety and trigger FDA enforcement actions.
Frequently Asked Questions
What is SCADA in cyber security?
SCADA cybersecurity protects supervisory control and data acquisition systems from cyber threats. It secures networks, devices, and protocols that monitor critical infrastructure, emphasizing operational availability and safety over data confidentiality.
How secure are SCADA systems?
Security varies widely based on system age and architecture. Legacy systems remain highly vulnerable due to outdated technology, while modern implementations with network segmentation, continuous monitoring, and strong access controls achieve robust protection.
What are the best practices for SCADA network security?
Best practices include:
- Network segmentation using the Purdue Model to isolate critical systems
- Zero Trust access controls with multi-factor authentication
- OT-aware monitoring tools that understand industrial protocols
- Regular assessments by qualified engineers with OT expertise
- Risk-based patch management for legacy equipment
- Incident response plans prioritizing operational continuity and safety


