What is the recommended secure remote access solutions for industrial operations?
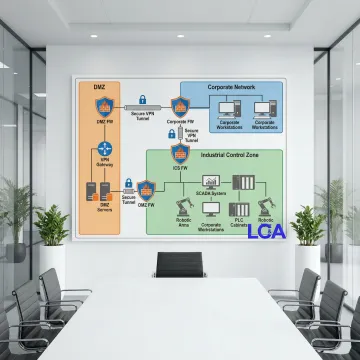
The recommended approach combines multiple security layers including encrypted VPN connections, multi-factor authentication, network segmentation to isolate critical systems, role-based access controls, real-time monitoring and logging, and regular security audits. We design solutions tailored to your specific industrial environment that balance robust security with operational needs.
What is the most secure method of remote access?
The most secure method implements a defense-in-depth strategy with encrypted VPN tunnels, multi-factor authentication requiring multiple verification methods, network segmentation to limit access scope, zero-trust architecture verifying every connection, continuous monitoring for suspicious activity, and regular security patches. This multi-layered approach significantly reduces vulnerability to cyber threats.
What is access control in industrial security?
Access control in industrial security refers to policies and technologies that regulate who can access specific systems, equipment, or data. This includes physical access controls, user authentication mechanisms, role-based permissions defining what actions users can perform, audit trails tracking all access attempts, and automated enforcement of security policies to protect critical manufacturing infrastructure from unauthorized access.
How quickly can secure remote access be implemented?
Implementation timelines vary based on your existing infrastructure and security requirements. A basic secure remote access system can typically be deployed in 2-4 weeks, while comprehensive enterprise solutions with full network segmentation and advanced monitoring may require 6-12 weeks. We conduct an initial assessment to provide an accurate timeline for your specific needs.
Will remote access affect my system performance?
Properly designed remote access solutions have minimal impact on system performance. We implement dedicated secure channels, optimize bandwidth usage, and use efficient encryption protocols. In many cases, remote access actually improves operational efficiency by enabling faster diagnostics, reducing travel time for troubleshooting, and allowing immediate response to issues.
What happens if there's a security breach attempt?
Our solutions include real-time intrusion detection systems that immediately identify and respond to breach attempts. Automated systems can block suspicious connections, alert security personnel, and log all details for investigation. We also provide incident response protocols and can assist with forensic analysis and remediation if needed.
Can remote access work with my existing control systems?
Yes, our solutions are designed to integrate with a wide range of existing industrial control systems, PLCs, SCADA systems, and HMIs from various manufacturers. As a Rockwell Systems Bronze Partner, we have deep expertise with Allen-Bradley and Rockwell platforms, but we regularly work with Siemens, Schneider Electric, Emerson, and other major industrial automation brands.
What ongoing maintenance is required?
Secure remote access systems require regular security updates, monitoring of access logs, periodic security assessments, and occasional credential management. We offer comprehensive maintenance packages that include continuous monitoring, automatic security patches, quarterly security reviews, and 24/7 support to ensure your systems remain protected against evolving threats.